SHA-1 breaks but PDF 2.0 deprecates it
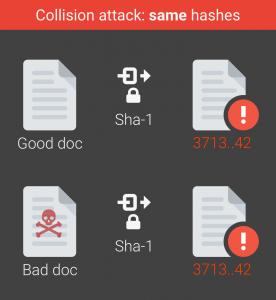
It is now proven that the contents of a PDF hashed with SHA-1 can be changed without invalidating the signature, with significant consequences for older software implementations.
 shattered.io reported on Thursday, February 23 that SHA-1, an industry cryptographic hash function standard, has been broken in practice.
shattered.io reported on Thursday, February 23 that SHA-1, an industry cryptographic hash function standard, has been broken in practice.
Quoted in Ars Technica, one of the lead researchers on the team that broke SHA-1, Marc Stephens, said:
"As an example of the insecurity of SHA1 [the identical-prefix collision] is very meaningful. Chosen-prefix collisions are more powerful and relieve an attacker from some constraints, but identical-prefix collisions can be just as dangerous with a very creative attacker. It is hard to say which things you can’t do with an identical-prefix collision.
But we do know quite some demonstrated threats using identical-prefix collisions: certificates with identical names and different pubkeys, PDF files, PostScript files, TIFF files, JPEG files, Word files, file archives, signed software, Email message/attachment PGP/GPG signatures."
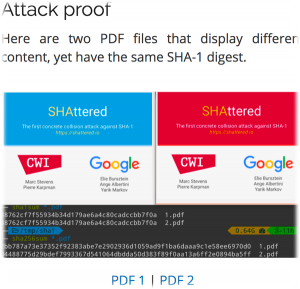
The attack proof provided by the team, and available from shattered.io, happens to use two PDF files that display different content, yet have the same SHA-1 digest.
PDF implementers should take note that ISO 32000-2 (PDF 2.0) deprecates SHA-1. PDF 2.0, which has been (mostly) final for a year now, is in its final editing phase now, and is expected before summer.
Are you implementing PDF 2.0? Consider joining us for the PDF 2.0 interop events, this coming May 2-3 in Cambridge, in the UK, and June 12-13, in Boston.




